In a personal consultation we will answer all your questions. If you wish you can receive our e-book for free!

For a secure digital world: data protection, information security and technical security in harmony for carefree data handling.
#data protection #information security #technical security
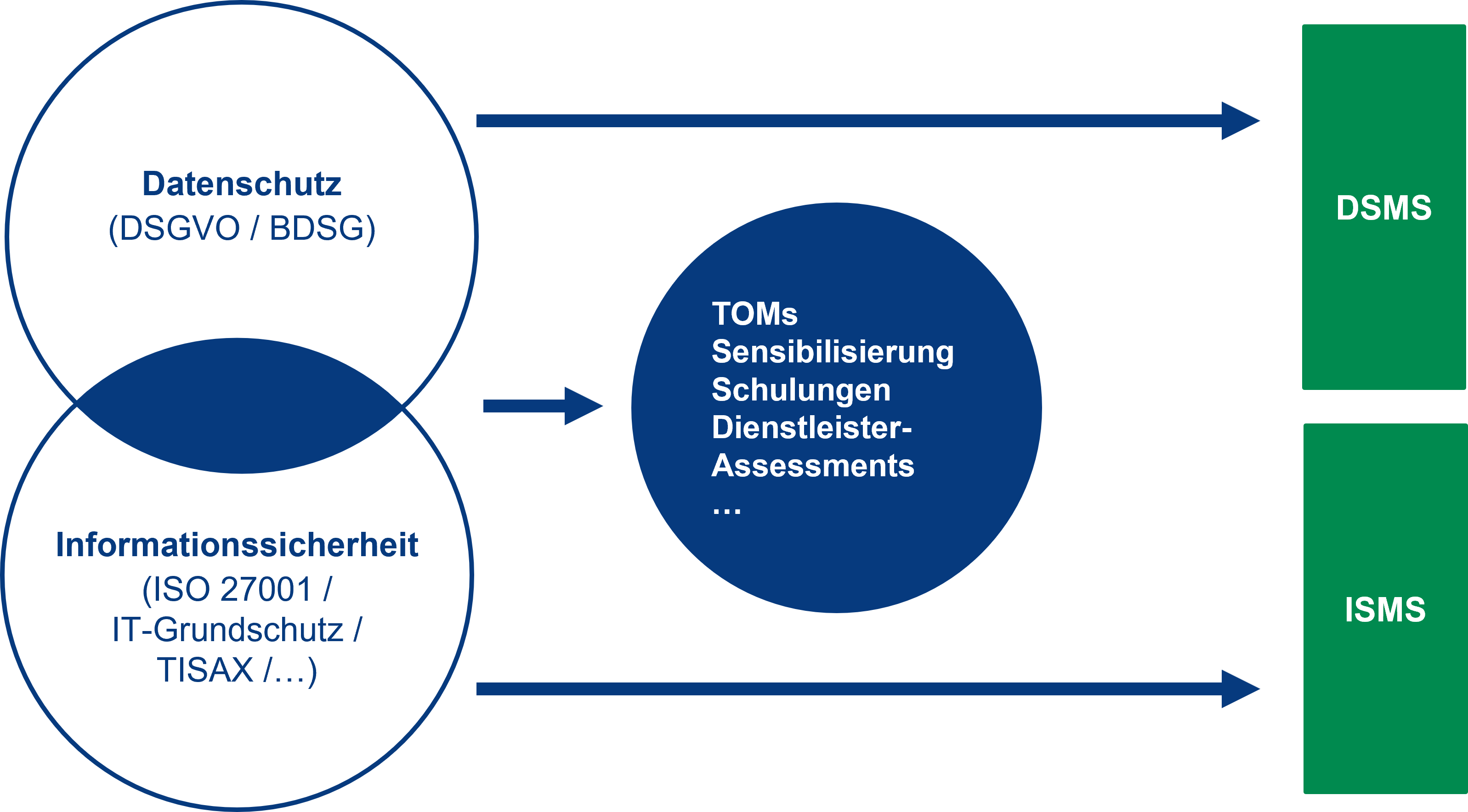
Data protection, information security and technical security are indispensable pillars in the digital age, enabling the protection of personal data, ensuring the confidentiality of information and protecting against threats to IT systems. Together they form a robust security foundation for organisations to minimise risks and gain the trust of customers and partners.
Competence Center Data Protection & Data Security.
Holistic security as we understand it - data protection by Bechtle.

Technical security.

- Focus audits and data protection checks offer a targeted review of data protection measures in a company.
- Data protection consulting supports companies in implementing and complying with the required data protection standards.
- An external data protection officer can help companies meet data protection requirements and ensure compliance.
- Mentoring and coaching are used to train and support internal data protection officers to effectively fulfil their role.
- Consulting, training and awareness measures help to raise awareness of data protection throughout the organisation.
- Data protection audits enable a comprehensive review of data protection practices to identify and address potential weaknesses.

- A cyber security check provides a comprehensive analysis of the IT infrastructure to identify potential vulnerabilities and threats and develop appropriate countermeasures.
- The implementation of ISM (information security management) systems enables organisations to structure and coordinate their security practices to protect confidential data.
- Consultancy, training and maturity testing help to increase an organisation's security level and sensitise employees to act consciously with regard to information security.
- An external IT security officer supports companies in planning, implementing and monitoring IT security measures to effectively ward off threats.
- ISO 27001 and BSI audits serve to prepare for certification processes and ensure that all relevant security standards are met in order to strengthen the trust of customers and partners.

- Vendor-independent consulting provides objective insights into technical security solutions to make the best possible security improvement decisions.
- Security analyses and pen testing make it possible to identify vulnerabilities in systems before they can be exploited by attackers.
- Privileged Access Management helps control and monitor access to sensitive systems to prevent unauthorised use.
- Phishing campaigns allow staff to respond to phishing emails in controlled environments to raise their awareness of security threats.
- Education, training and awareness measures sensitise employees to technical security practices and help promote security-conscious behaviour.
- Hack Academy events, also known as live hacks, provide hands-on insights into real hacking scenarios to deepen understanding of current threats and how to defend against them.
Bechtle relies on the AKARION Compliance Cloud.

- No IT implementation is required, saving time and resources.
- The solution is designed to be user-friendly to ensure easy and intuitive use.
- The solution is modular and can be adapted to individual requirements.
- By using this solution, costs and efforts can be reduced, leading to efficiency gains.
With the Akarion Compliance Cloud, our consultants can effectively dovetail data protection and information security and thus optimally meet the requirements of our customers. optimally fulfil the requirements of our customers. A win-win situation for all involved.
Frank Peter, Head of Data Protection and Data Security

*these fields are required.
Please read our Privacy Policy for information on how we process your data and protect your rights as da data subject.