Your personal account manager is happy to help. Get in touch.


Secure working from home starts with Zero-Trust.
Your path to Zero Trust.
Duo offers market-leading solutions that support you on your way to a complete Zero Trust security model. The reliable access solution delivers everything you need to protect your apps and data on a large scale.

Duo security solutions compliment every technical environment and have been developed to verify identities and to set up trusted devices regardless how, when or where the user logs in meaning you can prevent threats and attacks caused by compromised log in details.
Two-factor authentication.
Verify the identities of all users with effective, powerful authentication (two-factor authentication) before allowing access to enterprise applications and resources. Duo supports all MFA methods, such as: Mobile apps, push notifications, offline options, biometric-based WebAuthn, hardware token, and more.
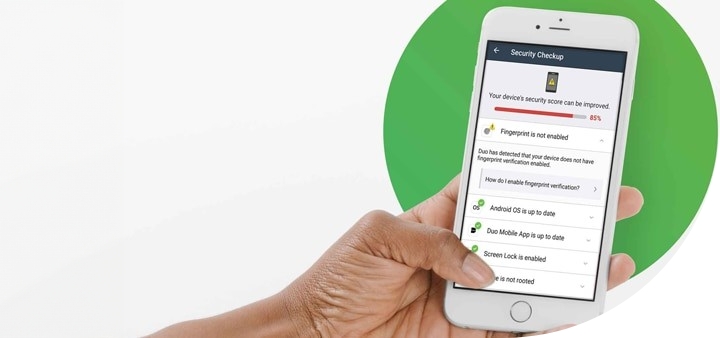
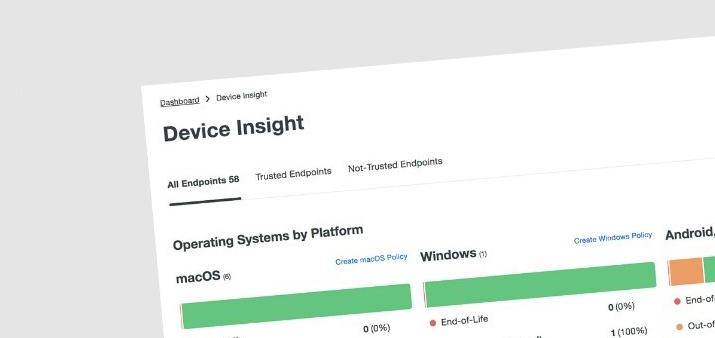
Gain an overview of all devices whether they are managed or not. This means that you can check if they meet your security standards before granting access. Duo offers a detailed overview of all your users’ devices and also gives you an insight into the state of their security.
The Duo platform gives you a comprehensive overview and control over BYOD by capturing and tracking every device accessing protected applications, including desktops, notebooks and mobile devices without the use of a mobile agent. You’ll receive detailed data and reports on user behaviour and any risky devices plus user, admin and telephony data to enable easy integration into existing SIEM (Security Information and Event Management) systems.

Protect every application by defining guidelines that limit user and device access to those that fulfil the company’s risk tolerance levels. Even location-based guidelines that allow access to applications to be allowed or denied depending on the location of the user or device are no problem.
Give users secure access to all protected applications (on-premise or cloud-based) via a uniform, seamless interface that can be accessed from anywhere. Duo also protects access to your remote access gateway provider, VPNs, VDIs and proxies such as Cisco AnyConnect, Juniper, F5, Citrix and more.
We use YouTube to embed video content on our website. This service may collect data on your activity. For more information, please go to the settings page.
Please not our privacy policy, which informs you comprehensively about our data processing and your privacy rights.
Source: The Total Economic Impact™ by Cisco Duo, a study commissioned by Forrester Consulting in February 2023. The results are based on a mix of different organizations.