


Cyber threats are on the rise – are you prepared?
Security challenges are growing rapidly – and so are the risks for your company. Cyber attacks are becoming more targeted, complex and consequential. This makes it all the more important to understand cyber security holistically and implement it effectively. We give you a clear overview of how you can identify and minimise risks and protect your IT in the long term with modern, state-of-the-art solutions.
Lectures and speaker.

When AI automates the psychology of attack.
Keynote
When language models meet human psychology, the threat landscape for businesses changes radically. Modern cyber attacks use the power of AI to individualise social engineering with minimal resource expenditure while scaling it up massively. Psychological vulnerabilities are systematically identified based on publicly available information about individuals and organisations, and attacks are optimised to fit perfectly – even unnoticed in subtle dialogues. Since these tactics are specifically targeted at business networks and social media, conventional technical protective measures often come to nothing. In this presentation, we analyse this new modus operandi and put the effectiveness of classic awareness training to the test: Is existing knowledge still sufficient to withstand these highly personalised threats, or do we need a completely new understanding of human resilience in the digital age?

Cyber security in turbulent times.
Roundtable Bechtle
How can companies maintain data sovereignty when dealing with American cloud providers? Which IT investments are truly necessary in economically challenging times – especially against the backdrop of regulatory requirements such as NIS2 and CRA? Let's discuss which strategies, priorities and next steps your company is currently planning.

Agentic AI: The future of cyber resilience.
Cisco
The digital attack surface is growing rapidly – new vulnerabilities arise every day. Traditional, manual security approaches are reaching their limits when it comes to effectively countering highly automated and AI-supported cyber attacks.
Agentic AI is revolutionising IT security: it enables autonomous security operations that proactively protect corporate resources in data centres and hybrid clouds and ensure long-term cyber resilience.
Join Charles Kionga, Principal Consultant at the Bechtle-BISS Competence Centre, as he presents groundbreaking technologies that are paving the way for a new era of IT security.

Live demo: Data carrier detection dog – How secure is your sensitive data really?
Schwarzwald Dogs
Experience the use of internationally certified data carrier detection dogs in our presentation with live demonstration.
Our dogs reliably detect even the smallest, professionally hidden data carriers and listening devices – quickly, discreetly and independently of technical infrastructure. See live how modern security concepts and animal precision come into play where traditional methods reach their limits.
An exclusive insight into data security at the highest level.

Compliance has not made us safer – only slower.
Roundtable Bechtle
Compliance is supposed to create security – but in everyday life, many organisations experience above all increasing complexity, growing documentation requirements and a high coordination effort. At the same time, the question remains as to how much actual security this creates.
In this roundtable, we will discuss where frameworks, audits and certifications offer real added value – and where they primarily fulfil formal requirements. The focus will be on sharing practical experiences and different perspectives on the balance between verifiability, efficiency and effective security work.


Command & Control Frameworks – Hacking in Reality.
Bechtle
Modern cyber attacks follow a clear pattern: after initially compromising a system, attackers establish a covert communication link – the command and control (C2) framework. This presentation provides insights into the actual tools and techniques used in professional cyber attacks and demonstrates live how C2 frameworks work in practice.


No Risk Management - No Fun!
TrendAI
Without smart risk management, digital innovation quickly becomes a blind flight. TrendAI Cyber Risk Exposure Management creates transparency and provides a clear basis for decision-making at management level, while operational IT risks are assessed and measures implemented. The presentation deliberately takes a strategic approach: high level, clear, relevant.

MFA & passwordless authentication as standard – access management as the foundation.
Pointsharp
Why centralised management of MFA options is key to a secure digital workplace. The real challenge begins when MFA needs not only to be enabled, but also centrally managed and supported by robust access management. Find out what really matters when it comes to a unified and secure solution.

Micro-VM isolation – unique protection when all else fails!
HP Inc.
HP Inc. demonstrates how critical processes can be reliably isolated using micro-VM isolation, even in the event of successful attacks. Experience how a unique security approach provides protection at the hardware level – exactly when it matters most.

Backup was yesterday – cyber resilience is today.
Dell
This presentation explains why traditional backup alone is no longer sufficient and how companies can use cyber resilience – including immutability, air-gap vaults, intelligent anomaly detection and clear recovery processes – to safeguard their business capabilities after an attack.

Bechtle
Passwords are broken, and so is classic MFA. Both have already been proven with Evilginx at Security Campus.
However, if you want phishing-resistant authentication or even passwordless authentication, you have to start with the basics: SSO.
This presentation uses practical examples and a live demo to show why MFA projects fail, how to conquer the authentication jungle, and why cyber security starts with usability. Caution: it could make your everyday work much easier...


When the enterprise app becomes the attacker: Understanding and preventing cloud-based identity attacks.
Bechtle
Attackers no longer need to steal passwords to gain access to data in the Microsoft 365 cloud. They use something much simpler: the trust of your employees. Through targeted phishing, they trick users into authorising seemingly harmless applications with far-reaching permissions – often completely unnoticed by security teams.
In this presentation, we will show how a manipulated enterprise application can be used to read and exfiltrate emails, files and identity information – without any classic account compromise. We will highlight a typical attack path, provide practical insights and explain how you can effectively prevent such attacks.

HPE Networking
Dynamic and flexible for every single connection. HPE Axis lays the foundation for a modern cloud era.
With the HPE SRX Firewall, consistent protection across borders with manageable complexity in modern infrastructures.

Bechtle
The implementation of the NIS2 Directive presents operational, organizational, and strategic challenges for 29,500 companies this year.
In this roundtable, we will jointly examine the key requirements of NIS2 implementation. The focus is on sharing practical experiences on topics such as registration and reporting obligations, risk and supplier management, as well as the challenges of efficient NIS2 implementation. Can compliance be designed not just as a regulatory burden, but as a true business enabler?

Darktrace
One attack, many targets: Why an air gap between IT and OT is not enough
Teaser: Attackers typically start with initial access in the IT environment and gradually expand their privileges until they reach systems connected to production. This progression exploits trust relationships, limited transparency, and the natural convergence between IT and operational environments. In this presentation, we show how Darktrace helps build a more resilient OT environment, supports security teams with contextualized analysis, and protects the entire digital landscape.

Rittal
The market for the construction and operation of data centres is under enormous pressure to innovate: the growing prevalence of AI applications is rapidly driving up the demand for computing power and efficiency. At the same time, legislators are demanding a clear reduction in energy consumption and a sustainable infrastructure with new regulations such as the Energy Efficiency Act (EnEfG).
To meet these challenges, operators are relying on technological innovations such as advanced cooling solutions, modular construction methods and the consistent use of renewable energies. The trends of 2026 and beyond are making data centres more powerful, sustainable and flexible – and thus fit for the demands of the digital future.
But what does this mean for your IT infrastructure? As a technology leader, Rittal is your expert partner for the entire IT lifecycle – from planning and implementation to modernisation.

Sophos
Sophos Workspace Protection combines zero trust network access, DNS layer security, email monitoring and a hardened, policy-controlled workspace browser into a consistent security layer – fully integrated into the Sophos Security Platform
for correlated telemetry and automated responses. At the same time, the solution helps organisations to specifically control and protect the use of new AI-based technologies in order to securely operate hybrid workloads, external user paths and modern AI-supported processes.

KeepIT
Today, companies use an average of over 120 SaaS applications – and that number is growing steadily. But data backup no longer ends with Microsoft 365.
As a leading SaaS backup provider from Denmark, Keepit recognised early on that modern IT strategies require much more comprehensive protection. Keepit has been backing up Microsoft 365 since 2017, followed shortly afterwards by Google Workspace and Salesforce. By mid-2025, eight workloads were supported – today there are already 14, with a clear roadmap for more.
These workloads are specifically selected and based on market requirements, regulatory requirements and compliance guidelines – with the aim of reliably securing the most business-critical applications.
In this presentation, you will learn which applications are currently protected, which ones will be added soon, and how Keepit technically implements broad and in-depth security – so that your company is optimally protected against SaaS outages, data loss, and attacks.

Watchguard
Seamless combination of continuous access control and 24/7 managed detection & response – for comprehensive threat detection and access security
At a time when hybrid working models and distributed infrastructures are creating new attack surfaces, traditional perimeter security is no longer sufficient. This presentation shows how the combination of zero trust and managed detection & response (MDR) enables a holistic protection concept: zero trust ensures continuous identity and context verification for every access, while MDR detects, analyses and automatically responds to threats around the clock. Together, these two approaches form a highly effective security ecosystem that makes companies more resilient to modern cyber attacks – without increasing operational complexity.

Rubrik
- Difference between traditional backup and cyber recovery/resilience
- Business continuity / emergency plan / minimum viable company
- Assume breach approach: How should I respond if I assume that the attacker is already inside my infrastructure?

Microsoft
Why ‘AI first, security second’ doesn't work and how modern security is becoming an enabler for productive and secure AI scenarios.

Cloudflare
Availability is the hardest currency in digitalisation. But current, high-volume DDoS waves targeting critical infrastructure show that traditional security stacks often become bottlenecks themselves.
Cloudflare is breaking this paradigm. At the Bechtle Cyber Security Campus 2026, we will show you how the Connectivity Cloud shifts security and performance directly to the edge. Learn how to secure your APIs, protect AI workflows from data leakage with AI gateways, and neutralise attacks in under 50 milliseconds.

Kaseya
The presentation ‘Prevention, Response, Awareness, Cyber Resilience – Easier than you think’ shows in a practical way how companies can strengthen their IT security in a comprehensive and understandable manner. Using concrete examples, it explains how pentesting detects vulnerabilities at an early stage, dark web monitoring identifies potential data leaks, modern EDR solutions detect and stop attacks in real time, and a well-thought-out backup strategy combined with business continuity planning ensures the ability to act in an emergency.
The aim is to convey cyber resilience not as a complex theory, but as a practical, structured concept that sensibly combines prevention, rapid response and sustainable security awareness.

Digicert
Today, digital trust means more than just issuing certificates – it's about controlling complexity, risks and regulatory requirements. As lifetimes shorten, attack surfaces grow and post-quantum readiness becomes a strategic necessity, PKI must evolve from a technical infrastructure to an enterprise-wide trust logic. The presentation shows how companies can systematically manage and automate trust, thereby increasing security, simplifying compliance and significantly reducing the total cost of trust.

Keeper
Cyber attacks in the DACH region are increasing in scope, frequency and complexity. This is putting IT decision-makers under increasing pressure to secure access to critical systems and stay one step ahead of compliance requirements such as NIS2 and DORA.
In this presentation, we highlight the biggest cybersecurity trends shaping the DACH landscape and show how modern, unified access controls can help you reduce risk, ensure business continuity and simplify your security stack.

Crowdstrike
The threat landscape in 2026 is characterised by increasingly fast and elusive adversaries, whose average time to breach has dropped to just 29 minutes. Learn how threat actors leverage AI, cross-domain attacks across endpoints, identity, cloud and SaaS, and abuse of trust in supply chains and cloud identities to bypass traditional security controls.

Yubico
Look forward to a live demo by Thomas Stahl on the magic of Yubico FIDO Pre-reg. We will show you how the user experience is redefined from the very first moment: plug-and-play instead of complicated setup processes. Participants will see first-hand how pre-registered hardware keys eliminate the frustration of initial setup and make the most secure login factor easier than ever before.

Mimecast
Insider threats pose ever-greater challenges for companies – whether through unintentional errors, malicious intent or a lack of awareness among employees. With the Mimecast Human Risk Management Platform, organisations can not only identify and minimise insider risks, but also strengthen their data security in the long term through targeted training and automated protective measures. Learn how to protect your sensitive company data and build strong security awareness within your team.


Bechtle CDC
As part of our Cyber Defence Centre, we take a look under the hood of modern security architectures. We demonstrate how Network Detection & Response (NDR) closes a critical visibility gap by passively analysing all network traffic without agents – especially where traditional EDR or SIEM approaches reach their limits, such as in OT environments.

Beyond Trust
Does everyone in your organisation really have only the permissions they actually need? This question was already difficult to answer in traditional IT environments with basic user management. However, with the increasing use of cloud services, hybrid infrastructures and automated workloads, the management of identities and permissions has become significantly more complex today. At the same time, the current threat landscape shows that over 90% of cyberattacks begin with compromised identities – for example, through phishing, social engineering or stolen login credentials.
In this presentation, BeyondTrust will demonstrate why identity security plays a central role in cyber defence today and how organisations can gain greater visibility and control over their privileged identities and access.
Together with Bechtle, a practical identity security risk assessment and accompanying demo will demonstrate how organisations can analyse their existing identity and access structures, highlight potential risks and identify specific areas for action.
Through practical use cases, discover how you can move from ‘flying blind’ when it comes to permissions to an effective identity security strategy, thereby reducing your attack surface, meeting compliance requirements and securing your IT environment in the long term.


NoSpamProxy
Traditional spam and quarantine folders are no longer appropriate in the modern email security landscape, as they are both unnecessary and legally problematic – emails are considered to have been delivered even whilst in quarantine. A more efficient approach is to scan incoming messages in full as soon as they are received and then make a clear decision on whether to accept or reject them. The Level of Trust Engine helps to minimise false positives whilst significantly increasing security and transparency.


NoSpamProxy
The presentation examines current email scams, including domain impersonation and targeted attacks such as CEO fraud. It demonstrates how NoSpamProxy comprehensively analyses incoming messages as soon as they are received and, using modern security technologies, reliably detects even sophisticated attack scenarios.
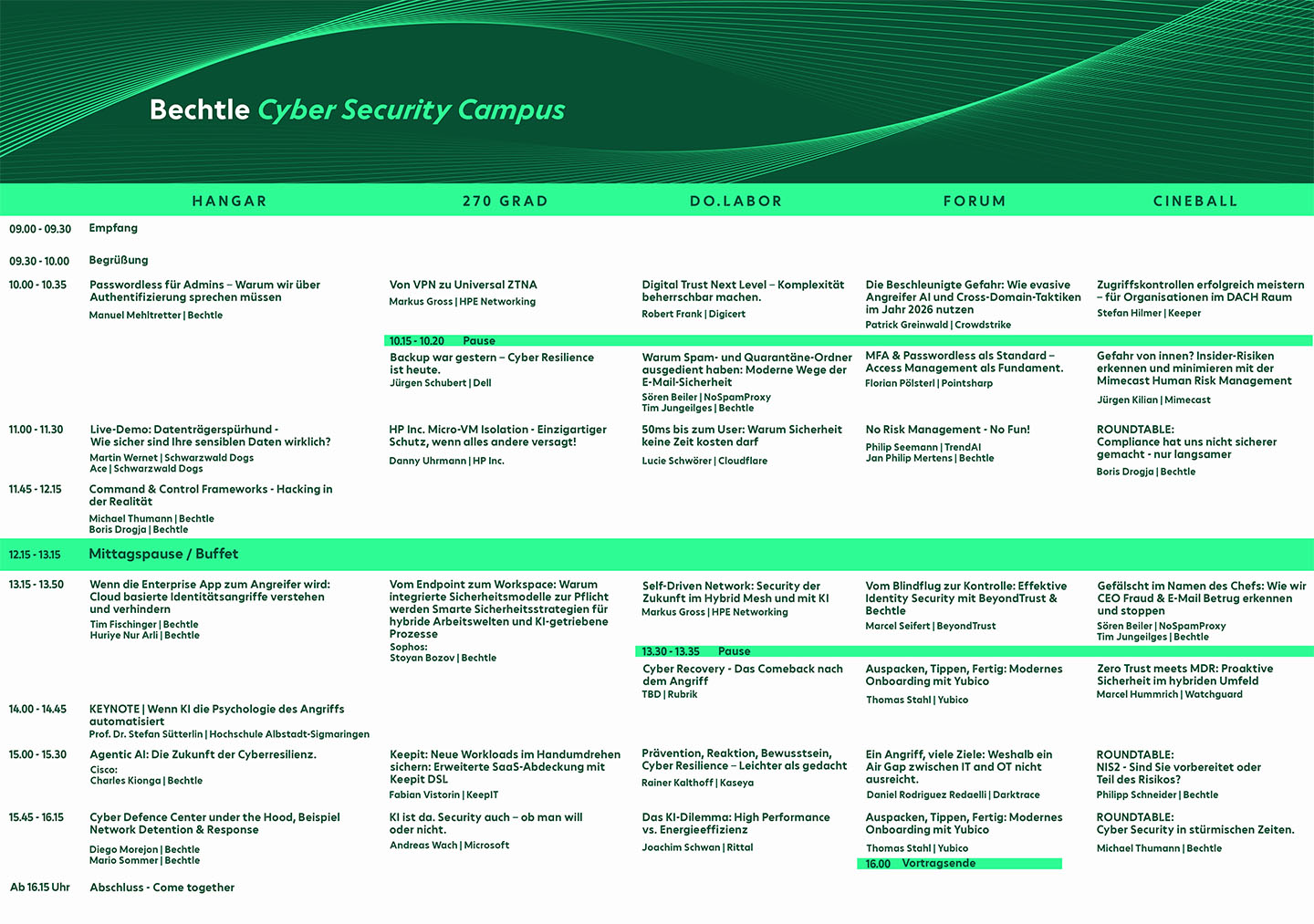
Agenda.
Manufacturer.

